User guide
Finding your way around the guide
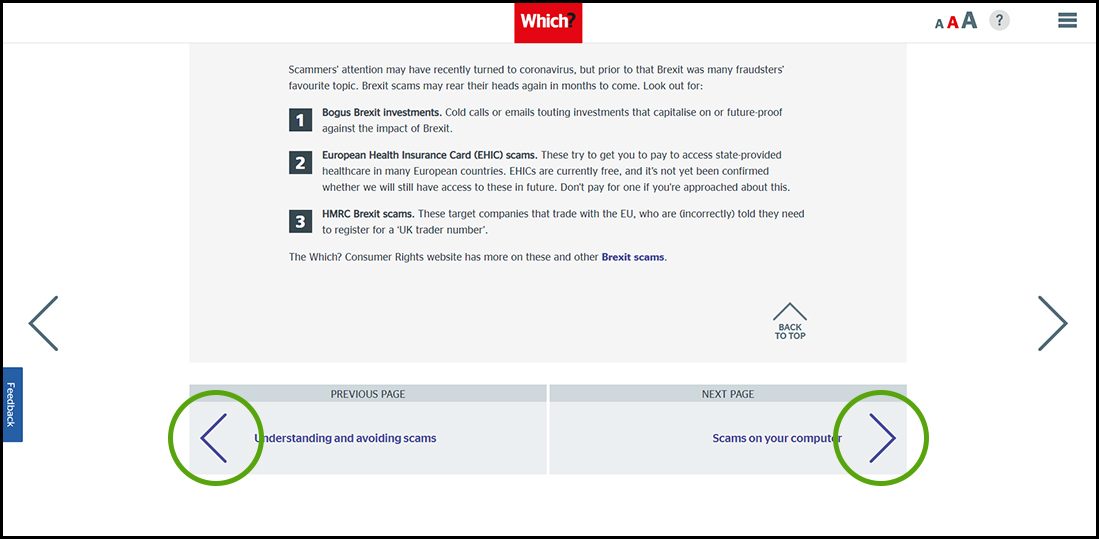
To navigate between pages, click or tap the arrows to go forwards to the next page or backwards to the previous one. The arrows can be found either side of the page and at the bottom, too (circled in green, below).

Menu/table of contents
Click or tap on the three horizontal lines in the top-right of your screen to open the main menu/table of contents. This icon is always visible whether you're using a computer, tablet or smartphone. The menu will open on top of the page you’re on. Click on any section title to visit that section. Click the cross at any time to close the table of contents.
Text size
On a computer, you'll see three different sized letter 'A's in the top-right of your screen. On a smartphone or tablet these are visible when you open the menu (see above). If you’re having trouble reading the guide, click or tap on each of the different 'A's to change the size of the text to suit you.
Pictures
On some images you'll see a blue double-ended arrow icon. Clicking or tapping on this will expand the picture so you can see more detail. Click or tap on the blue cross to close the expanded image.
Where we think a group of images will be most useful to you, we've grouped them together in an image gallery. Simply use the blue left and right arrows to scroll through the carousel of pictures.
Links
If you see a word or phrase that's bold and dark blue, you can click or tap on it to find out more. The relevant website will open in a new tab.
Jargon
If you see a word or phrase underlined, click or tap on the word and small window will pop up with a short explanation. Close this pop-up by clicking or tapping the cross in the corner.
Help
On a computer, you'll see a question mark icon in the top-right of your screen. On a smartphone or tablet this is visible when you open the menu (see above).
Clicking or tapping on the question mark will open this user guide. It opens on top of the page you're on and you can close it any time by clicking or tapping the cross in the top-right corner.

Scams on your computer
An unprotected computer can be a gold mine for criminals. Find out why security software is so important and how to evade the hackers.
Some computer scams take the form of malicious content like a fake shopping site – visit our site to learn how to spot these. Others originate with a phishing email or scam call and end with your computer being held to ransom. You can check if your accounts have been compromised in a data breach, leaving them vulnerable to scams at haveibeenpwned.com.
Our scam alerts service sends advice on scams direct to your inbox.
Pop-up messages
You’re browsing online when up pops a worrying message claiming your computer is infected with viruses. Such pop-ups aren’t generated by your security software, nor by a real computer scan, it’s just fearmongering to get you to click a dodgy ‘scan’ button, call a phone number or pay for a protection plan.
Clicking on the link could install malware, any protection plan won't exist, and calling the number could go through to a fake tech support service. Don't call any numbers or click on any links if you’re not sure the pop-up is from your installed security software. Get to know what genuine messages from your security software look like, so you can spot fake pop-ups.
Avoid clicking on the ‘X’ to close the pop-up window – it could download malware. Instead, press Ctrl + Shift + Esc in Windows to see what programs you have open and fully close your web browser. Most web browsers’ privacy or security settings let you block pop-ups. (In Chrome, for example, click the three dots icon in the top-right corner, click Settings then Privacy and security/Site settings. Click Pop-ups and redirects and turn the setting to Blocked.)
Do
• Always go to websites by typing the address or URL into the browser yourself.
• Contact your bank immediately if you find charges on your account that you don’t recognise.
• Use security software and keep it up to date.
• Use strong passwords and a password manager to safely store logins.
• Report anything suspicious to the relevant company and appropriate authorities – see Reporting scams.
Don't
• Enter personal information into sites you’re not sure are genuine.
• Download forms or other attachments from unsolicited emails.
• Feel pressured into responding to alarmist emails or pop-ups about security problems or fines.
• Pay any attention to ads about gift cards or discounts or other ‘too good to be true’ offers.
• Click on anything in a pop-up that you suspect could be a scam.
Ransomware
Ransomware RansomwareMalware designed to block access to a computer system unless you pay to release it. pop-ups are the result of malware having been installed on your computer, maybe after you clicked on a malicious link. Blackmailers use a virus to lock your computer or otherwise deny you access to your own files, then demand payment for re-access. They may claim to be from the police and say they’ve found evidence of illegal activity on your computer to shame you into paying the fine.
Never pay up; it will just give the blackmailers money that could be used to fund other criminal activities, and there’s no guarantee they will release your computer.
Some, but not all, forms of ransomware can be resolved with anti-malware tools. Failing this, you may be able to start your computer in safe mode and carry out a system restore. Visit our site to find out how to remove ransomware viruses.
Suspicious ads
The internet is chockablock with advertising. While most is legitimate, ad panels and pop-ups are another route in for scammers. As our experts explain on our site, Google, Facebook and other social media sites are popular spaces for fraudsters to place their lures, though dodgy ads can appear on any site that takes advertising. We’ve spotted Bitcoin scam ads on dating sites, for example, and shopping sites can be rife with fake listings (see Online marketplace scams).
Adware AdwareSoftware that can add pop ups or adverts to web browsing. pop-ups exist between acceptable software and malware. Adware is software that generates pop-up ads for products that can be legitimate, but may be of dubious value, and the ads can be annoying. Adware can be downloaded by accident when downloading a program (for example, from a download site, as they often don't disclose who they partner with). Adware can be hard to uninstall, but anti-adware tools such as Malwarebytes’ AdwCleaner can help.
Hacking
Hacking involves someone gaining access to a protected system. This can be done simply by a hacker working out your password. Password-cracking tools can make this straightforward if your password isn’t strong enough. Hackers may also use social engineering tactics to persuade you to reveal security details, through phishing, vishing VishingPhishing via a phone call. (phone phishing) or smishing Smishing Phishing via SMS (mobile text message). (text message phishing) tactics. They may combine this with password-cracking software and/or information that you publish on social media profiles to put together a fuller profile. You can protect yourself from hacking with a strong password – see Understanding and avoiding scams for more.
Fraudsters may also hack into the email of an organisation you know, such as a solicitor, and email bills to their contacts. Always check with the organisation before paying an emailed invoice with new bank details.
For £5 a month, you can access phone and email advice to keep your computer and other technology running smoothly. Our tech gurus can help with anything from the best security software to how to avoid online scams. You’ll also receive Which? Computing, the UK’s biggest computing magazine. Find out more on our site.